Keycloak vs Zitadel
Learn how Keycloak and Zitadel differ in their key features, development activity, technology
stack and community adoption, so you can decide which of these authentication & sso providers is best for you.
Learn how Keycloak and Zitadel differ in their key features, development activity, technology stack and community adoption, so you can decide which of these authentication & sso providers is best for you.
Keycloak
Stars
34,834Forks
8,459Last commit
10 hours agoRepository age
13 yearsLicense
Apache-2.0
Auto-fetched .

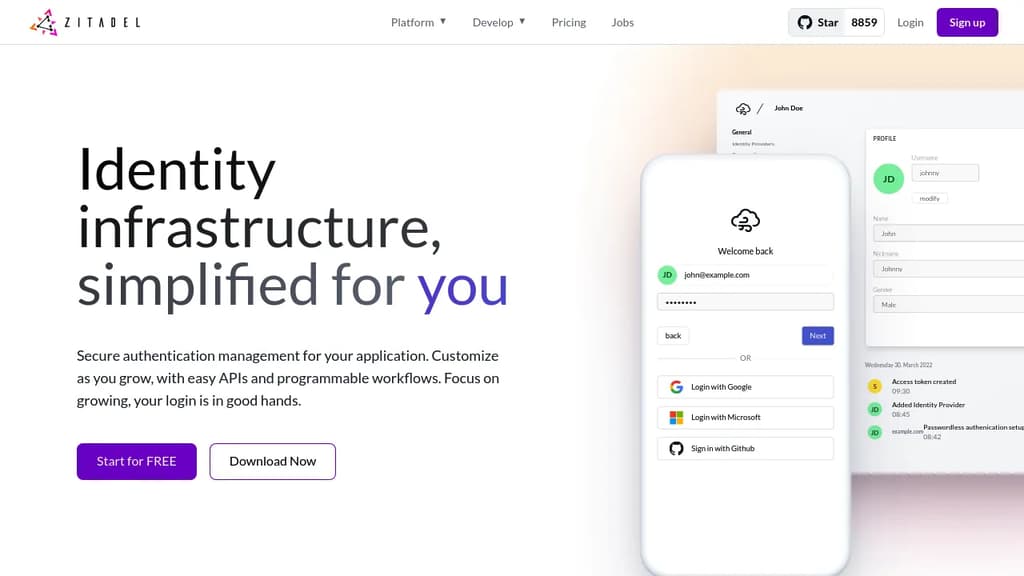
Zitadel
Auto-fetched .
Detailed Comparison
Both Keycloak and Zitadel have their unique strengths and serve similar purposes effectively. Consider your specific needs regarding popularity, activity, technology, maturity, licensing and features when making your decision.
Both Keycloak and Zitadel have their unique strengths and serve similar purposes effectively. Consider your specific needs regarding popularity, activity, technology, maturity, licensing and features when making your decision.
Community & Popularity
Keycloak leads in popularity with 34,834 stars vs 13,992 stars for Zitadel. The 149% higher star count indicates stronger community adoption. In terms of developer contributions, Keycloak has 8,459 forks, indicating strong developer engagement.
Development Activity
Both projects show recent activity, with Keycloak last updated 10 hours ago and Zitadel 13 hours ago.
Technology Stack
Both tools share common technology foundations, being built with JavaScript, CSS, Bash, Typescript, JSX. However, they differ in their additional technology choices: Keycloak uses Python, C, Java while Zitadel leverages Next.js, SCSS, Golang, Lua.
Project Maturity
Keycloak has been in development longer, starting 13 years ago, compared to Zitadel which began 6 years ago. This 6.8-year head start suggests Keycloak may have more mature features and established processes.
Licensing
The projects use different licenses: Keycloak is licensed under Apache-2.0 while Zitadel uses AGPL-3.0. Consider the licensing requirements when choosing for your project.
Use Cases & Features
Both tools serve similar use cases in Authentication & SSO, Authorization & Permissions.
Hosting & Deployment
Zitadel provides self-hosting options for complete data control and customization, while Keycloak may be primarily cloud-based or require different deployment approaches.
Other tool comparisons to consider
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs
vs