Open Source Cerbos Alternatives
A curated collection of the 6 best open source alternatives to Cerbos.
The best open source alternative to Cerbos is Keycloak. If that doesn't suit you, we've compiled a ranked list of other open source Cerbos alternatives to help you find a suitable replacement. Other interesting open source alternatives to Cerbos are: Authentik, Zitadel, Ory, and Stack Auth.
Cerbos alternatives are mainly Authorization & Permissions Tools but may also be Authentication & SSO Providers. Browse these if you want a narrower list of alternatives or looking for a specific functionality of Cerbos.
Written by Piotr Kulpinski
Comprehensive open source identity management solution offering single sign-on, social login, and fine-grained authorization for applications and services.

Keycloak simplifies application security by providing a complete identity and access management solution. With built-in single sign-on (SSO), users authenticate once to access multiple applications, eliminating repetitive logins and logouts.
The platform offers robust identity features including:
- Social login integration with popular providers
- LDAP and Active Directory federation
- OpenID Connect, OAuth 2.0, and SAML 2.0 protocol support
- Fine-grained authorization policies
- Two-factor authentication
- User account management
Administrators benefit from a centralized console to manage users, configure authentication flows, and set security policies. Users get a self-service portal to manage their profiles, passwords, and linked accounts.
Enterprise-ready capabilities include high performance, clustering support for scalability, customizable themes, and extensive APIs for integration. As a Cloud Native Computing Foundation project, Keycloak maintains high standards for security, reliability, and community-driven development.
Looking for open source alternatives to other popular services? Check out other posts in the alternatives series and openalternative.co, a directory of open source software with filters for tags and alternatives for easy browsing and discovery.
authentik is an open-source identity provider that offers self-hosted authentication, authorization, and user management for businesses of all sizes.
authentik is a powerful, open-source identity and access management solution designed to give organizations full control over their authentication and authorization needs. Here's why authentik stands out:
-
Self-hosted and Open Source:
- Deploy anywhere, maintaining complete control over your sensitive data
- Continuously reviewed by community experts, ensuring transparency and security
-
Flexible and Customizable:
- Pre-built workflows for quick setup
- Fully customizable authentication steps through configurable templates
- Comprehensive APIs for advanced automation
-
Enterprise-Grade Features:
- Multi-factor authentication (MFA)
- Conditional access
- Application proxy
- Support for multiple protocols (SAML2, OAuth2, OIDC, SCIM, LDAP, RADIUS)
-
Scalable and Easy to Deploy:
- Supports Kubernetes, Terraform, and Docker Compose
- Designed for both B2B and B2C use cases
-
Comprehensive Identity Solution:
- Authentication
- User enrollment
- Self-service capabilities
-
Cost-Effective:
- Streamlined pricing with no hidden costs
- Core functionality included without extra charges
authentik empowers organizations to prioritize security, simplify deployment, and automate identity workflows. Whether you're a small business or a large enterprise, authentik provides the tools and flexibility to meet your specific identity and access management needs.
ZITADEL provides a comprehensive identity management solution with easy APIs, customizable workflows, and serverless deployment options.
ZITADEL is an all-in-one identity suite designed to streamline application development with robust authentication and authorization capabilities.
Key features:
- Customizable hosted login: Easily authenticate users with a branded, customizable login page
- Modern authentication methods: Support for SSO, social logins, and multi-factor authentication
- Role-based access control: Assign permissions based on user roles for granular authorization
- Multi-tenant architecture: Built-in support for B2B scenarios with organization management
- Extensibility: Customize workflows and integrate ZITADEL into existing systems with Actions
- Developer-friendly: Modern APIs (gRPC and REST) with comprehensive documentation
- Flexible deployment: Run ZITADEL as a managed service or self-host for full control
ZITADEL empowers developers to offload complex identity tasks while maintaining adaptability. With security defaults and custom code extensions, it provides a solid foundation for building scalable applications with sophisticated user management.
Whether you need authentication for a small project or enterprise-grade identity infrastructure, ZITADEL offers the flexibility to grow with your needs. Focus on building your core product features while ZITADEL handles the intricacies of identity management.
Ory is a certified and battle-tested identity solution backed by a large open source community and trusted by Fortune 500 companies.
Ory provides a modern and modular approach to identity and access management (IAM) that scales, offers unmatched user experience and deployment flexibility, and only charges for what is used.
Key benefits of Ory include:
- Uninterrupted performance even under demanding conditions, ensuring no revenue loss during peak demand
- Comprehensive visibility and fully configurable options to balance user experience, privacy and security
- Unmatched flexibility for customization beyond just branding, including UI, workflows, standards, deployment, scale and security
- Integrations and SDKs for all modern and legacy frameworks
- Migration guides to easily move from home-grown or other IAM solutions
- Trusted by over 30,000 companies, from startups to Fortune 500 enterprises
- Available as open source, self-hosted, or fully managed cloud offering
Ory allows you to build a unified identity system that meets all your needs, whether you're looking for authentication, authorization, user management, or a complete IAM platform. With options for self-hosting or using the managed Ory Network, you can get started quickly and scale seamlessly as your needs grow.
Stack Auth provides secure authentication, authorization, and user management for developers in just 5 minutes.
Stack Auth is the open-source alternative to Auth0, offering a comprehensive authentication and user management solution for developers. With Stack Auth, you can implement secure authentication, authorization, and user management features in your applications in just 5 minutes.
Key benefits of Stack Auth include:
- Quick setup: Get started with authentication in your Next.js project using the setup wizard.
- Beautiful integration: Enjoy lean and responsive design with pre-styled components that developers and users will love.
- Flexible implementation: Choose between headless or headful UI options to fit your project needs.
- Advanced features: Benefit from password authentication, SSO, 2FA, organizations & teams, permissions & RBAC, and more.
- Developer-friendly: Built for developers, Stack Auth is simple to understand, use, and integrate into your tech stack.
- Open-source and self-hostable: Maintain full control over your authentication infrastructure.
Stack Auth provides a REST API and client/server SDKs for custom integrations. It also offers features like user impersonation for debugging and webhooks for syncing with other services.
With its open-source nature and developer-first approach, Stack Auth offers a powerful, flexible, and cost-effective solution for authentication and user management in your applications.
Open-source authorization service for implementing fine-grained access controls. Centralized, scalable solution supporting RBAC, ABAC and ReBAC with Google Zanzibar-inspired architecture.
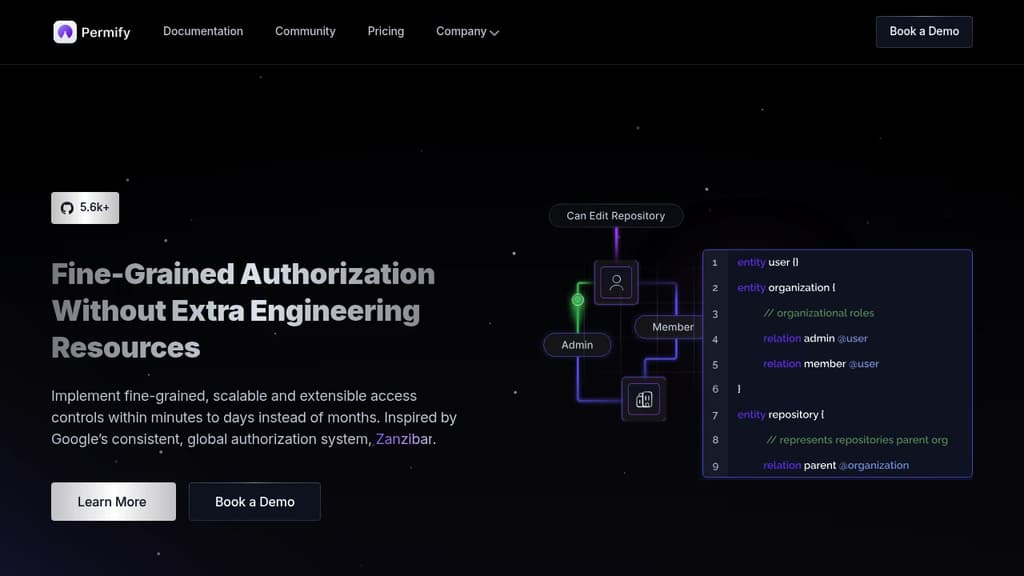
Centralized authorization service that transforms how you implement access controls across your applications. Instead of embedding authorization logic in your codebase, Permify provides a dedicated service that handles all permission checks and policy management.
Key capabilities include:
- Fine-grained permissions supporting RBAC, ABAC, and ReBAC models
- Flexible authorization language for building granular policies without steep learning curves
- Real-time data synchronization for dynamic access checks across your entire stack
- Permission database inspired by Google Zanzibar for blazing fast response times
- Comprehensive APIs for access checks, data filtering, and permission management
The platform centralizes permission data as structured relationships, enabling efficient management of large data volumes while maintaining consistent authorization policies across multiple applications. This approach eliminates development bottlenecks and allows teams to test, debug, and iterate authorization logic independently from application code.
Built for scalability, Permify handles complex permission scenarios while providing the performance needed for enterprise applications. The service integrates seamlessly with existing systems through well-documented APIs and supports various authentication patterns.